Hacker-Trained AI Discovers 16 New 0-Day Vulnerabilities in PDF Engines
Our researchers found 3 critical vulnerabilities in PDF ecosystems. Then we let our trained AI loose, and found 13 more.

Our researchers found 3 critical vulnerabilities in PDF ecosystems. Then we let our trained AI loose, and found 13 more.
Notes:
This research was done under responsible disclosure and with the full cooperation of Foxit and Apryse. Coordination and remediation efforts were conducted with the affected vendors prior to publication. Don’t test systems you don’t own or have explicit permission to access.
We would like to thank Foxit for their remarkable cooperation in the process of reporting and mitigating these vulnerabilities. Foxit is a prime example of how a vendor should handle and manage such incidents.
Research Findings: 16 verified vulnerabilities in PDF engines
Historically, Portable Document Formats – the immutable, localized PDF – was once considered a “safe” component inside enterprise environments. That is no longer the case.
To demonstrate how PDF services and engines can be exploited, we used Novee’s proprietary, multi-agent LLM system to uncover vulnerability patterns, and systematically scale them into a broad discovery campaign across two PDF vendor ecosystems.
The research uncovered 16 verified vulnerabilities across client-side PDF viewers, embedded plugins, and server-side PDF services.
❗An important factor to note: this research is not based on open source code, meaning this investigation relied on a true black-box approach. Finding vulnerabilities without access to source code is how many attackers operate – and so, it’s how we operate too.
The research demonstrated multiple exploit vectors, that could:
- Start with a document, URL, or embedded message
- Traverse client-side UI state, iframe boundaries, or postMessage handlers
- Reach dangerous sinks such as DOM XSS, internal network fetches, filesystem access, and OS command execution
Rather than isolated bugs, the issues cluster around recurring architectural failures in how PDF platforms handle untrusted input across layers.
Potential outcomes of exploitation include:
- One-click Account Takeover when PDF viewers are embedded in authenticated applications
- Persistent cross-user compromise, where a malicious document affects every subsequent viewer
- Backend remote code execution in PDF SDK components used by enterprise platforms
In multiple cases, a single malicious PDF or crafted URL was enough to trigger code execution under a trusted origin or backend service.
Note: If you would like the full deep-dive into our findings and methodology, read the unabridged research report.
Setting Our Sights on PDF Exploitability
Thanks to enriched features and a push for interactivity, modern PDF engines and cloud viewer platforms now combine:
- JavaScript and WebAssembly rendering engines
- Cross-origin iframes and embedded plugins
- postMessage-based initialization and configuration
- Server-side rendering, conversion, signing, and collaboration services.
These systems accept untrusted input from PDFs, URLs, query parameters, and messages, and then propagate that input across multiple execution contexts. In short, each data transition creates a trust boundary.
And, as Novee Research shows, in many cases those boundaries were crossed without proper validation.
Finding Vulnerabilities at Scale: How Novee’s AI Pentesting Platform Looks at PDFs from a Hacker’s Perspective
For the purposes of this research, we focused on two PDF ecosystems:
- Apryse WebViewer (PDFTron) — a React iframe UI combined with a complex JS/WASM engine and optional server components.
- Foxit PDF cloud services — multiple embedded plugins, iframe boundaries, postMessage flows, and extensive client-side logic.
Methodology: A Hybrid Human / Agent Approach
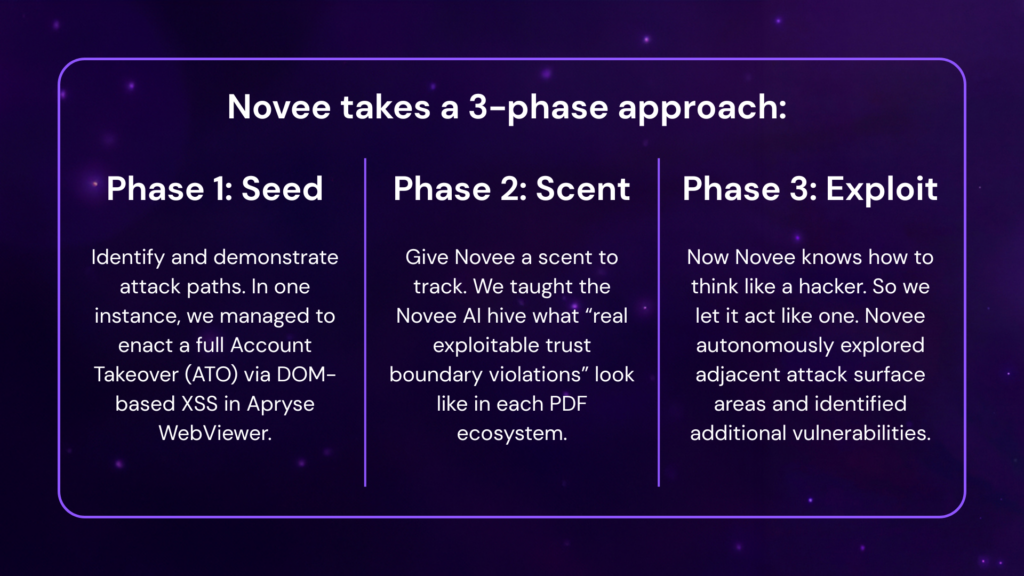
In Phase 1, our researchers manually identified 3 foundational vulnerability patterns. In Phase 2, the “hive” of Novee agents then learned how to find these same structural patterns. Once the agents internalized the “scent,” in Phase 3 they autonomously explored the massive attack surface of both Apryse and Foxit.
As a result, the Novee AI discovered 13 new exploitable vulnerabilities, in addition to the 3 found by our researchers.
Phase 1: Seed Vulnerabilities (Training Signals)
Note: For a full technical deep dive into our discovery process, read the full research report.
To understand how Novee researchers identified trust boundaries – and how to exploit them – we need to understand some of the architecture of our first research partner, Apryse WebViewer:
The user interface of Apryse is a WebViewer UI Layer. The UI is a prebuilt React SPA that loads inside an iframe, at paths such as:
/res/webviewer/<version>/ui/index.html
The Security Problem: This UI accepts configuration from multiple untrusted sources:
- query string parameters
- postMessage from the embedding page
- remote JSON configuration files
- LocalStorage + URL fragments
Since the entire UI runs inside an iframe, any input crossing into it must be validated.
Now let’s break down how we manually found the first of three CVEs, culminating in multiple fields reaching a DOM sink without sanitization, and leading to a one-click account takeover.
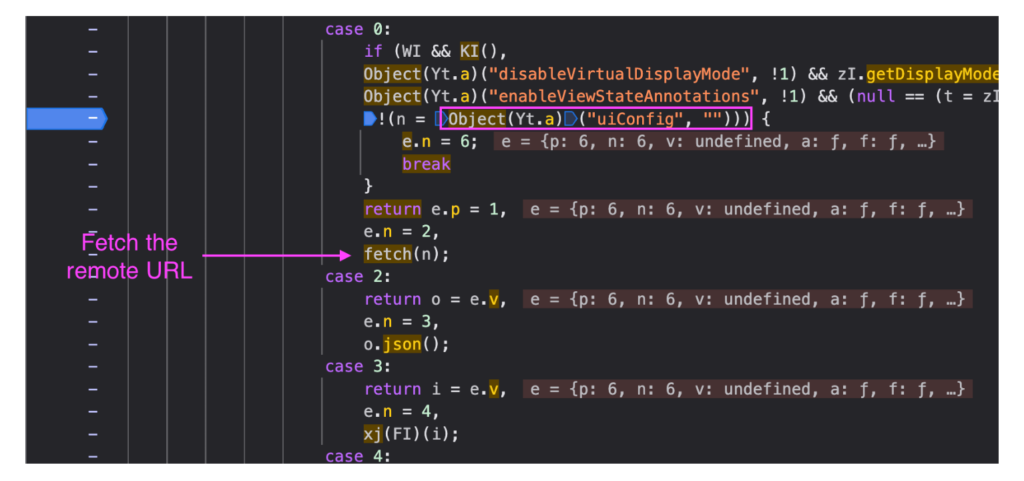
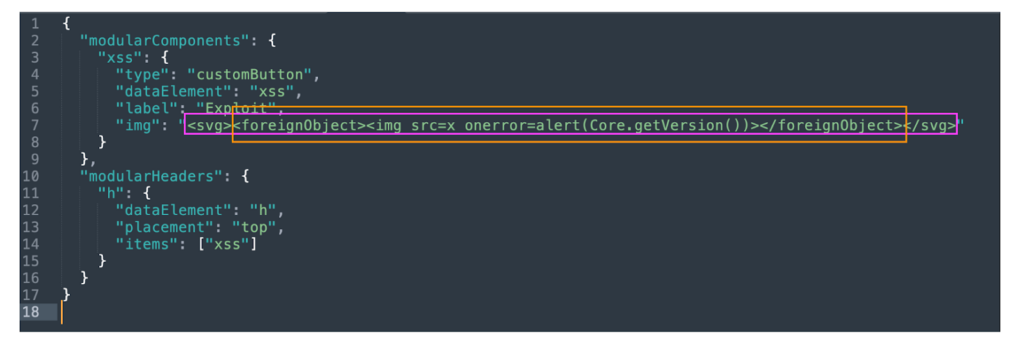
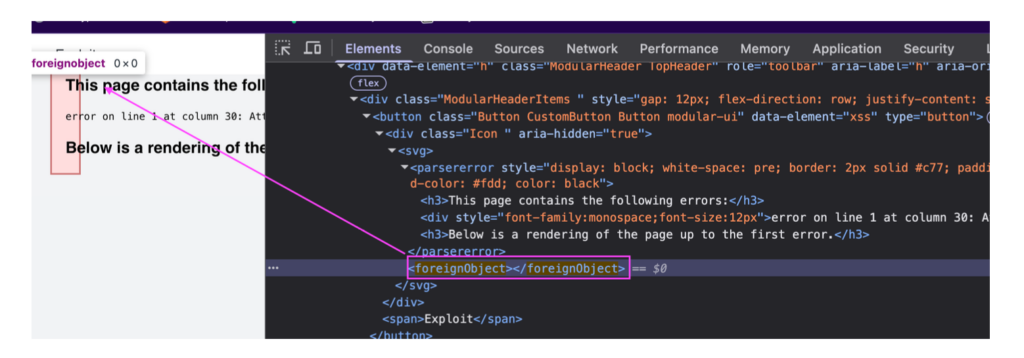
Finding CVE-2025-7042 – DOM XSS via Remote UI Configuration (uiConfig) – A One-Click Account Takeover
The Bug
The WebViewer UI accepts a uiConfig query parameter.
The Exploit
The query parameter – fully attacker-controlled – dictates where to fetch a “trusted” configuration, which influences how the DOM is built.
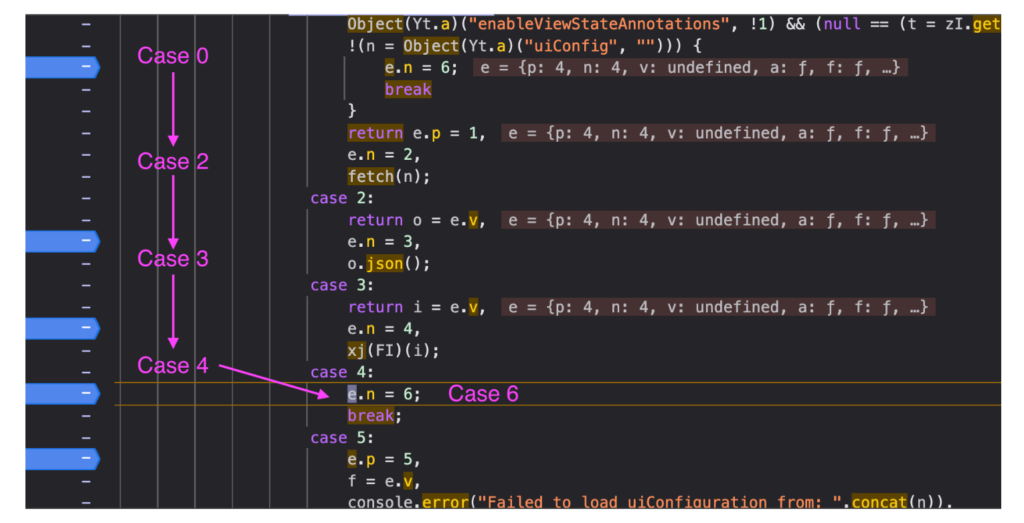
The Potential Impact
Existing XSS protections sanitize SVG elements but NOT HTML content inside of working payloads. When the browser encounters the payload, it switches from SVG parsing context to HTML parsing context, and HTML event handlers are preserved and executed.
We manage to execute a one-click account takeover using this exploit.
Phase 2: Give Novee’s AI Hacker the Scent
Strip away the specific payloads and code paths of all initial CVEs discovered by our researchers, and you will find the same structural failures:
- Untrusted input accepted without validation
- Data flows across trust boundaries without sanitization
- Culmination at a dangerous sink, e.g. DOM, network, file system
To autonomously search for similar vulnerabilities, our researchers gave the hive of Novee AI agents the “scent” – the broad structural failures implicit in PDF vulnerabilities. The multi-agent model worked as a team to replicate the researchers’ method:
- one agent enumerated high-impact sinks and traces backward to build complete source-to-sink chains
- a second agent resolved the hard parts static tools can’t prove in minified, dynamic code (dispatch, validation gates, middleware)
- a third agent turned confirmed chains into working PoCs under real trigger conditions.
Novee AI autonomously mapped the vendors’ massive attack surface and repeated the playbook at machine scale – turning a handful of seeds into 13 new verified vulnerabilities.
Phase 3: The Hunt Begins (Autonomous Exploration and Scale)
After internalizing these patterns, Novee autonomously explored adjacent attack surface areas and identified additional vulnerabilities — by applying the same reasoning to different parameters, endpoints, and plugins.
Some examples include:
- OS Command Injection in Foxit PDF SDK for Web Demo environment
- Three Reflected XSS Vulnerabilities in na1.foxitesign.foxit.com
- Stored XSS (WAF Bypass) via Collaboration feature in webviewer-demo.foxit.com
👉 For the full list of findings, see our full report.
Key findings include:
- DOM-based cross-site scripting via remote configuration, annotations, and message handlers
- Server-side request forgery with built-in data exfiltration channels
- Path traversal in backend collaboration and file-handling services
- OS command injection in PDF SDK backend components
Several vulnerabilities were exploitable with a single request and affected trusted domains, commonly embedded inside enterprise applications.
How to Give AI an Advantage in Vulnerability Discovery
It takes intuition, patience, and deep technical insight to discover any one of the three vulnerabilities found manually by our researchers.
And while we swear by their talent, we also acknowledge their limitations: could our researchers find every instance of a similarly structured vulnerability? Could they replicate their success, day-in, day-out, in a constantly changing codebase?
The easy answer is to turn to automated scanners and static tools. But SAST and CPG-based tools only work when the program follows a strict set of guidelines. Modern web products, like Apryse and Foxit, aren’t written like neat textbooks to reference. Their structures shift, imports are resolved in runtime, fragmented URLs and remote JSON enter codebases, and dangerous sinks are hidden by framework.
The truth is, static tools are powerful until the code stops being static.
Most “AI vulnerability discovery” efforts collapse because:
- they optimize for volume over correctness
- they hallucinate
- they don’t differentiate theoretical vs exploitable
- they lack a learning loop
Faced with dynamic code paths and real trigger conditions, most tools would stop trying to find an exploit, or at best, guess where one might be found.
Novee AI doesn’t give up, and it doesn’t need to guess, because behind our team of human researchers is a hive of AI agents, specialized and designed to replicate their intuition, experience, and persistence.
This approach enabled the discovery of high-impact vulnerabilities at scale, demonstrating how exploit reasoning can be systematized and applied across large, complex PDF platforms rather than remaining confined to one-off manual analysis.
Final Thoughts
The takeaway: This research did not rely on generic AI prompts or scanning heuristics, but on compiling the mental playbook of our elite vulnerability researchers into the AI agents themselves – allowing source-to-sink reasoning, mitigation analysis, and exploit validation to be executed systematically at scale.
This approach exemplifies the shortcomings of static, point-in-time security testing tools in uncovering exploitability in previously-thought “safe” enterprise systems. Modern web products’ structures shift, their imports are resolved in runtime, fragmented URLs and remote JSON enter their codebases, and dangerous sinks are hidden by framework.
Traditional tooling struggles in these environments because they assume determinism and linear code paths. Attackers do not.
For a full write-up of our research, read the technical report.
See what else continuous AI penetration testing can uncover. Explore our platform.