AI Pentesting: Security Testing that Works the Way Real Attackers Do
Testing tools and services today optimize for reports, audits, and checkboxes, not for answering the only question that actually matters: “Can someone break into my system right now?”

What is AI Penetration Testing?
AI penetration testing uses autonomous AI agents to simulate real attackers continuously, not episodically. Unlike traditional penetration tests that happen once or twice a year, AI pentesting operates persistently.
Autonomous AI agents plan, execute, and adapt penetration testing actions without relying on predefined scripts or static workflows. AI Pentesting works by:
- Mapping your attack surface from the outside in
- Identifying novel vulnerabilities and attack paths
- Validating exploitability with working proof-of-concept exploits
- Providing precise remediation guidance
AI Pentesting Solves the Impossible Choice of Security Tests
Before AI penetration testing, offensive security teams were forced into a false tradeoff between:
Manual penetration testing
Pros: gives you human intuition, creative exploitation, and the ability to uncover novel exploits by following business logic flaws.
Cons: doesn’t scale. It’s episodic, expensive, and reports are outdated days after the test is complete.
Automated scanners
Pros: find instances of known patterns, flag known CVEs, and surface theoretical risks at scale.
Cons: promise continuous coverage, but lack understanding of your business logic or environment – flooding you with false positives and surface-level results without validating what’s truly exploitable.
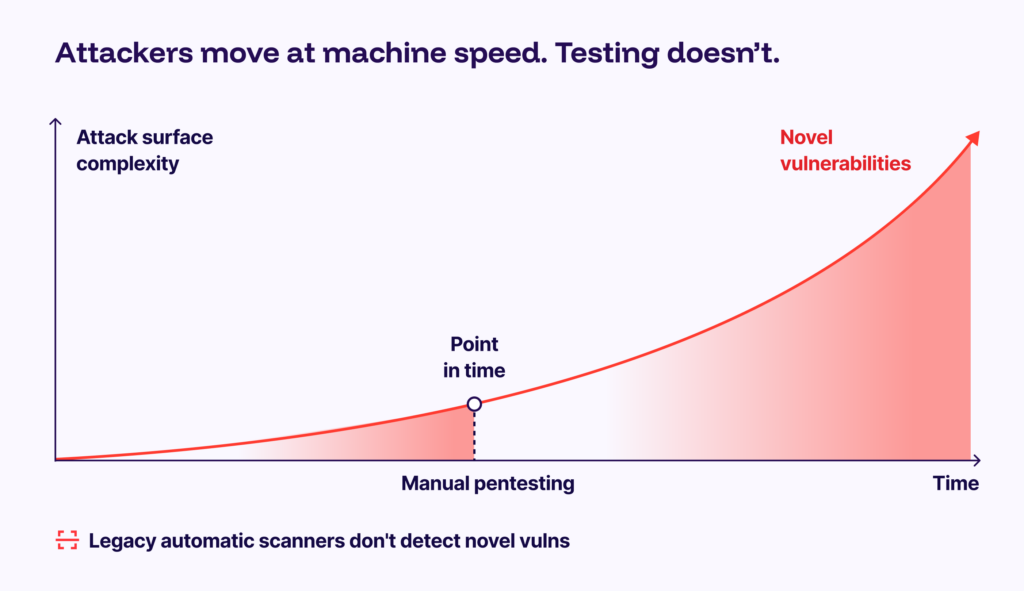
AI pentesting gives you all the benefits of manual, human-run testing, with none of the scaling issues. It’s as good as a manual pentesting, in just a few clicks.
How it Works
AI penetration testing relies on a battery of specialized agents, who continuously map live software environments the way an attacker would. They interact with real flows, tap real endpoints, and expose logic flaws in real behavior.
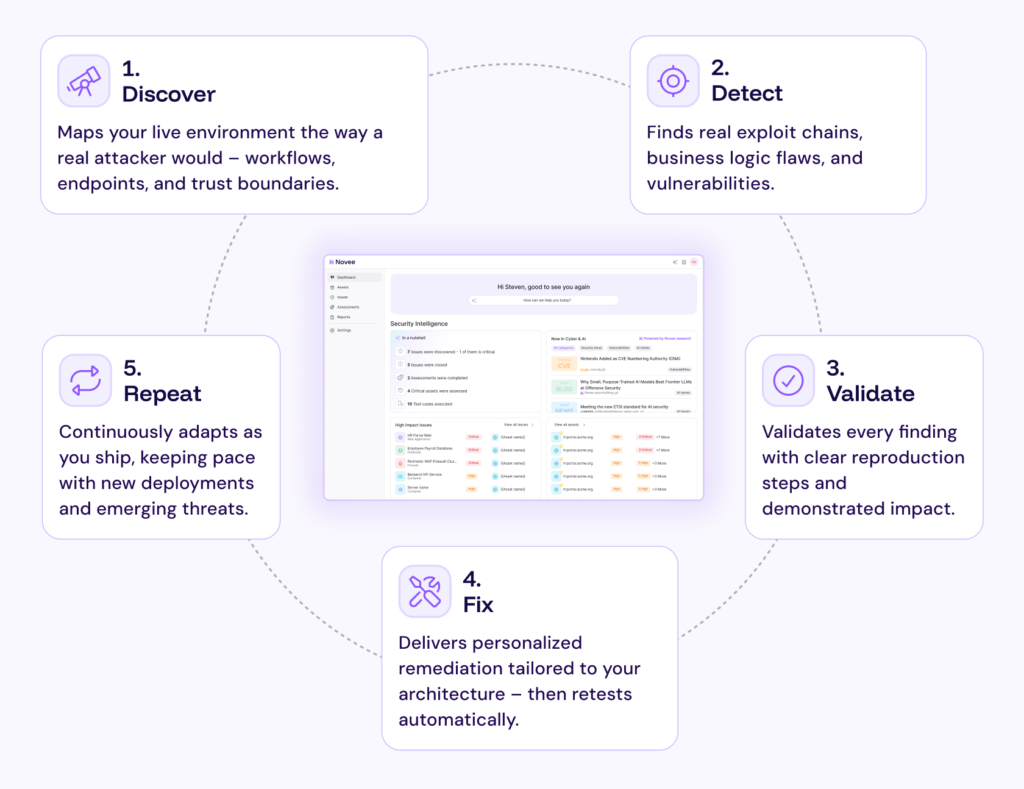
Setting up an assessment usually requires providing an application name, URL, and some level of credentials (for privilege escalation testing). Truly black-box AI pentesting needs nothing but an application name and URL (more on this below).
The AI pentester discovers all application entry points and generates unique test cases (which may or may not result in an exploitable issue), and then highlights what those issues are. The coverage map shows different testing areas, allowing users to see not only where issues were found, but also test cases that ran without finding an issue, indicating areas of defense strength.
From there, adept AI pentesting tools can close the loop by providing replication steps and even remediation guidance.
AI Penetration Testing Methodologies
AI penetration testing can follow different methodologies depending on the level of access and the threat model being simulated. Like traditional pentesting, it spans black-box, gray-box, and white-box approaches, but executes them continuously and adaptively.
Black-Box Testing
Black-box AI pentesting starts with no internal knowledge; often just a domain or application URL.
Autonomous agents discover exposed assets, enumerate endpoints, and probe live behavior from the outside in. This approach reveals externally exploitable weaknesses, emergent behaviors, and chained attack paths without relying on assumptions about how the system is designed.
It answers: What can an attacker reach and exploit right now?
Gray-Box and White-Box Testing
With partial or full access – such as authenticated credentials or architectural context – AI agents can test deeper authorization logic, privilege escalation paths, and complex workflows.
The focus remains the same: validate exploitability in a live environment, not just surface theoretical weaknesses.
Continuous Adversarial Method
Unlike episodic pentests, AI penetration testing runs continuously.
Agents:
- Generate hypotheses based on observed behavior
- Adapt based on system responses
- Chain small weaknesses into meaningful exploits
- Learn from failed attempts
This methodology mirrors how skilled attackers operate — probing, learning, and adapting — rather than executing static scripts or signature-based checks.
The Benefits of Thinking Like an Attacker
AI penetration testing functions like an expert red team – the kind with deep offensive tradecraft, the intuition to spot novel attack paths, and the creativity to chain small weaknesses into real exploits – working on your environment continuously.
AI Pentesting architecture typically includes:
- A reasoning core that determines what to test next, based on prior outcomes
- Memory and context that persist across actions and sessions
- Tool orchestration to select and sequence reconnaissance, exploitation, and post-exploitation techniques
- Feedback loops that refine strategy as the system encounters defenses or unexpected states
This approach mirrors how skilled human attackers operate; probing, learning, chaining, and adapting, rather than how scanners or scripted tools behave.
Meaningful Discovery, Clear Remediation, and Fewer Vulnerabilities
AI penetration tests are focused on revealing real, exploitable vulnerabilities across code environments, and giving code owners actionable remediation advice.
Real Risk Reduction at Speed
- Uncover verified, exploitable, non-CVE vulnerabilities – including zero days.
- Generate security findings indicating proven risks with clear fixes, and strengthen security posture day-over-day as coverage compounds
Clear, Actionable Remediation
- Produce clear, technical and top-level reports highlighting all potential attack paths and vulnerabilities.
- Generate precise fixes tailored to your architecture.
- Prompt automatic retesting after remediation.